Payment card-skimming malware targeting 4 sites found on Heroku cloud platform

Payment card skimmers have hit four online merchants with help from Heroku, a cloud provider owned by Salesforce, a researcher has found.
Heroku is a cloud platform designed to make things easier for users to build, maintain, and deliver online services. It turns out that the service also makes things easier for crooks to run skimmers that target third-party sites.
On Wednesday, Jérôme Segura, director of threat intelligence at security provider Malwarebytes, said he found a rash of skimmers hosted on Heroku. The hackers behind the scheme not only used the service to host their skimmer infrastructure and deliver it to targeted sites. They also used Heroku to store stolen credit-card data. Heroku administrators suspended the accounts and removed the skimmers within an hour of being notified, Segura told Ars.
This is not the first time cloud services have been abused by payment card skimmers. In April, Malwarebytes documented similar abuse on Github. Two months later, the security provider reported skimmers hosted on Amazon S3 buckets. Abusing a cloud provider makes good sense from a crook’s point of view. It’s often free, saves the hassle of registering look-alike domain names, and delivers top-notch availability and bandwidth.
“We will likely continue to observe Web skimmers abusing more cloud services as they are a cheap (even free) commodity they can discard when finished using it,” Segura wrote in Wednesday’s post.
In an email, Segura documented four free Heroku accounts hosting scripts that targeted four third-party merchants. They were:
- stark-gorge-44782.herokuapp[.]com used against shopping site correcttoes[.]com
- ancient-savannah-86049[.]herokuapp[.]com/configration.js used against panafoto[.]com
- pure-peak-91770[.]herokuapp[.]com/intregration.js was used against alashancashmere[.]com
- aqueous-scrubland-51318[.]herokuapp[.]com/configuration.js was used against amapur.]de
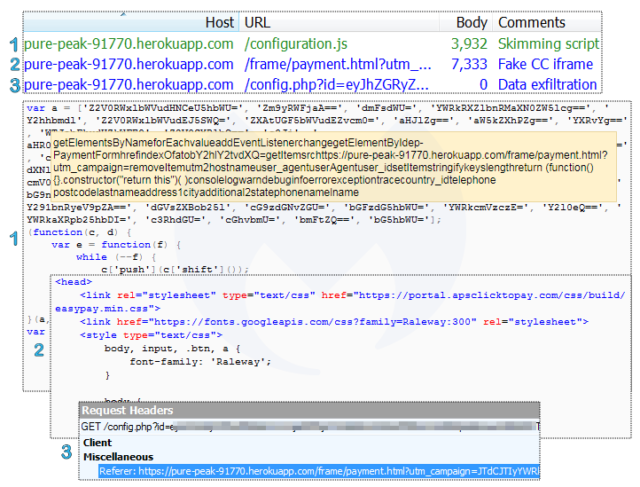
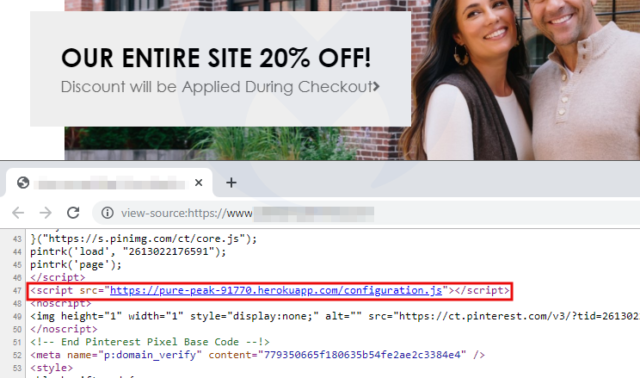
Besides setting up the Heroku accounts and deploying the skimmer code and data-collection systems, the scheme required compromising the websites of the targeted merchants through means that are currently unknown (although some of the sites were running unpatched Web apps). Attackers then injected a single line of code into the compromised sites. The injected JavaScript, which was hosted on Heroku, would monitor the current page for the Base64-encoded string “Y2hlY2tvdXQ=”—which translates to “checkout.”
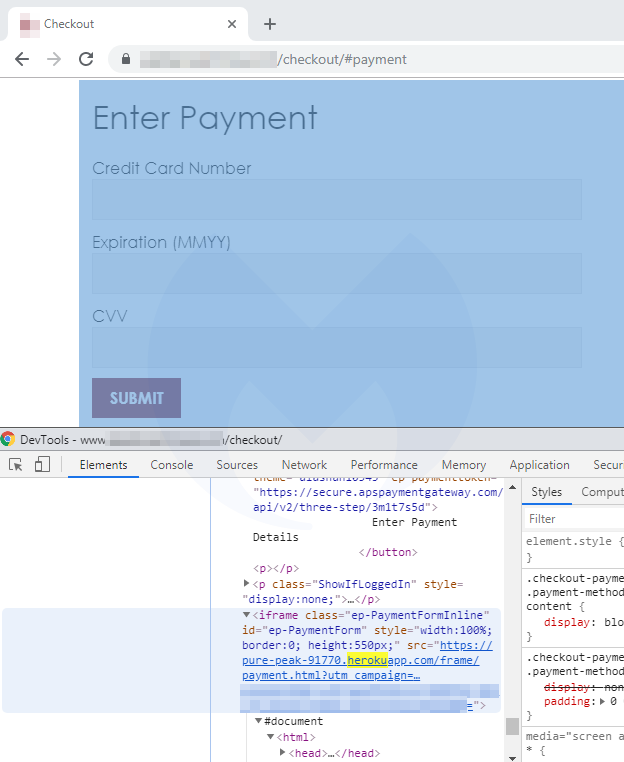
When the string was detected, the malicious JavaScript loaded an iframe that skimmed the payment-card data and sent it, encoded in Base64 format, to the Heroku account. The iframe-induced skimmer included an overlay on top of the legitimate payment form that looked identical to the real one. Below are three screenshots that show the scheme in action:
Segura said that Web searches suggest that the skimmers were hosted on Heroku for about a week. He wasn’t the only one to notice them.
Another one on @heroku
hxxps://stark-gorge-44782.herokuapp[.]com/integration.js. Fake form in an iframe. Data goes to hxxps://stark-gorge-44782.herokuapp[.]com/config.php?id= pic.twitter.com/Xa1F2z1Z1a
— Denis (@unmaskparasites) December 2, 2019
It’s not easy for the average end user to detect skimmers like the ones Segura has documented. Once the card data is exfiltrated, users will receive an error message instructing them to reload the page, but these types of errors happen often enough on legitimate sites that they wouldn’t be an obvious sign of fraud. And in any event, by the time the message appears, the card has already been compromised. More advanced users who want to know if they were compromised can get logs or Web caches for the four Heroku links listed above.
https://arstechnica.com/?p=1627923