Botnet of more than 17 million devices dismantled
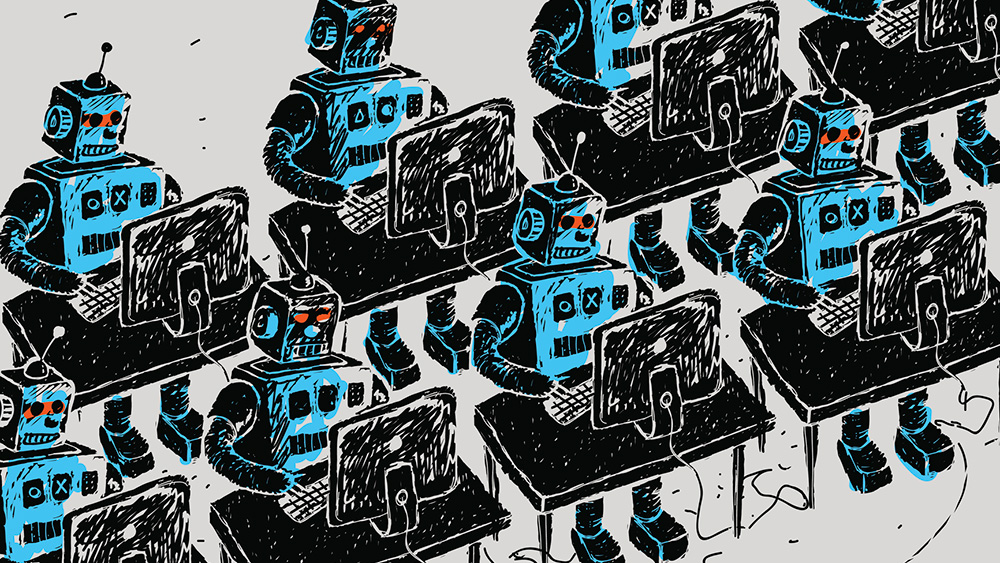
Authorities in the Netherlands said they dismantled a botnet that comprised more than 17 million devices and were managed by 200 servers in a joint operation by the police and the National Cyber Security Center.
The action, announced Thursday, came about after a security researcher reported the sprawling network to authorities. The host infrastructure was located in the Netherlands.
Used for criminal purposes
“The police then seized several botnet servers from a hosting provider for investigation,” the NCSC said. “The botnet was taken offline by the provider because it was used for criminal purposes.”
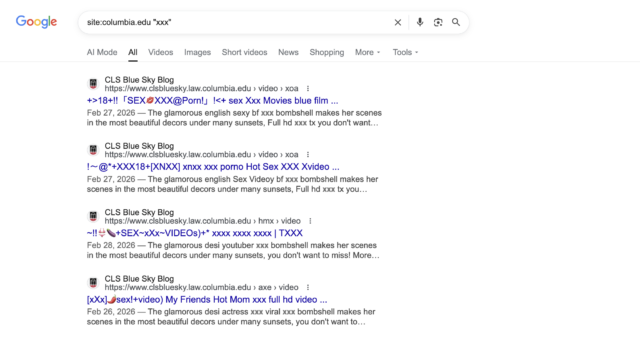
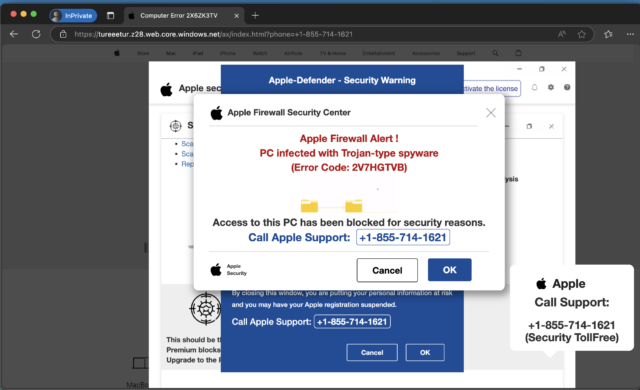
According to a report Thursday by the NL Times, the botnet was linked to ASOCKS, a Russia-based company that provides residential proxy services. These services cater to people and organizations who want to obscure their locations or identities by proxying their Internet traffic through third-party devices. Proxy services are often used for illicit or unethical purposes such as performing DDoS attacks, running botnet command-and-control servers, operating phishing operations, and scraping website content.
Ars was unable to independently confirm the NL Times report, but the claim checks out. Thursday’s NCSC post linked to a separate post that the nonprofit organization published a day earlier. That post, in turn, was updated to add a link to Thursday’s post. Wednesday’s post, headlined “Residential proxies and their major impact on digital security in the Netherlands,” warned: “Residential proxies are used to maintain anonymity and circumvent geographical restrictions. In this way, a Dutch organization can be attacked with Dutch proxies that have similarities with ‘regular’ traffic, making cybercrime mitigation more difficult.”
https://arstechnica.com/security/2026/05/botnet-of-more-than-17-million-devices-dismantled/