Azure Services SSRF Vulnerabilities Exposed Internal Endpoints, Sensitive Data
Cloud security company Orca has published details on four server-side request forgery (SSRF) vulnerabilities impacting different Azure services, including two bugs that could have been exploited without authentication.
SSRF flaws, Orca explains, typically allow attackers to access the host’s IMDS (Cloud Instance Metadata Service), enabling them to view information such as hostnames, MAC addresses, and security groups.
Furthermore, such security defects could be exploited to retrieve tokens, execute code remotely, and move to another host.
Impacting Azure Functions and Azure Digital Twins, the two unauthenticated vulnerabilities could be exploited without an Azure account to send requests on behalf of the server.
The remaining two security issues, which were identified in Azure API Management and Azure Machine Learning, require authentication for successful exploitation.
All four vulnerabilities are non-blind SSRF (full SSRF) issues, allowing an attacker to fetch any request and retrieve the output, Orca’s researchers say. Such flaws can typically be exploited via XXE (XML external entity), SVG files, a proxy, PDF rendering, vulnerable query string in the URL, and more.
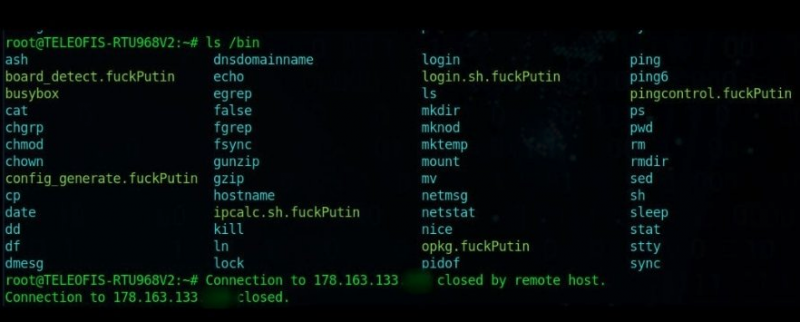
“The discovered Azure SSRF vulnerabilities allowed an attacker to scan local ports, find new services, endpoints, and sensitive files – providing valuable information on possibly vulnerable servers and services to exploit for initial entry and the location of sensitive information to target,” Orca says.
The issues could be exploited to request any URL by abusing the server, but various mitigations that Microsoft has implemented prevented the researchers from exploiting the newly identified bugs to reach IMDS endpoints.
The unauthenticated flaw in the Azure DigitalTwins Explorer service was caused by a bug in the user input validation following a request, while the issue impacting the Azure Functions service resided in a NodeJS based function.
The authenticated vulnerability in Azure API Management allowed the researchers to enumerate all open ports on the vulnerable server, review all of them, and retrieve more sensitive data, including Git client version, the empty refs list, and the git-scm capabilities.
The Azure Machine Learning service bug, Orca says, allowed the researchers to retrieve any endpoint.
Orca reported the vulnerabilities to Microsoft between October and December 2022. Patches were released shortly after each report, with the last vulnerability addressed on December 20.
UPDATE: Microsoft has published its own blog post, clarifying that the vulnerabilities were “low risk as they do not allow access to sensitive information or Azure backend services.”
Related: Microsoft Patches Vulnerability Allowing Full Access to Azure Service Fabric Clusters
Related: Azure Service Fabric Vulnerability Can Lead to Cluster Takeover
Related: Microsoft Azure Vulnerability Allowed Code Execution, Data Theft
https://www.securityweek.com/azure-services-ssrf-vulnerabilities-exposed-internal-endpoints-sensitive-data