Vulnerability management has two major components: discovering vulnerabilities, and mitigating those vulnerabilities. The first component is pointless without the second component. So, for example, Equifax, WannaCry, NotPetya, and many other breaches — if not most breaches — are down to a failure to patch, which is really a failure in vulnerability management.
In these examples the vulnerabilities were known, but not mitigated. Patches were available, but not implemented. It’s a hugely complicated problem, because although there are vulnerability management platforms, immediate patching is not always possible (for fear of breaking essential applications); and the ramifications of not patching are not easily understood.
“Everyone does vulnerability management,” says Illumio’s VP of product management, Matthew Glenn. “It’s like motherhood and apple pie — it’s just something you have to do.” So, companies have a vulnerability team that scans for and locates vulnerabilities, and then that team tries to persuade the app team to patch the vulnerable application.
“This creates a really interesting tension,” he continued, “because app teams really just want to make sure that their apps are running without interruption, while patching can create an unknown outcome. It takes time to get a patch installed. So, if they can’t install a patch, they look for some form of compensating control.”
Micro-segmentation firm Illumio is now seeking to provide that compensating control to this problem via a relationship with the Qualys vulnerability platform. Illumio already has a dependency mapping capability, called Illumination, as part of its Adaptive Security Platform. This shows dependencies and connections between different applications, even when spread across multiple data centers or in the cloud. It highlights whether connections are within policy, allowing companies to micro-segment the infrastructure to increase security.
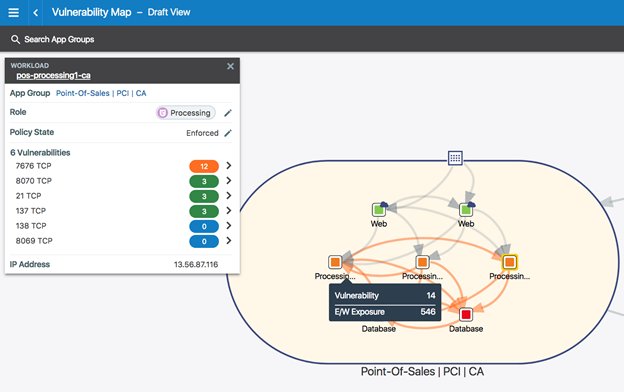
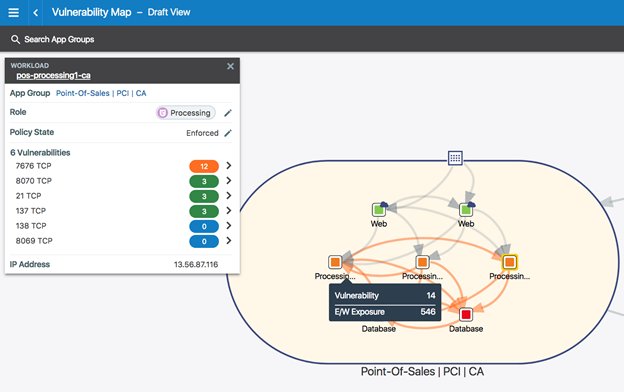
“What we’ve now added,” explains Glenn, “is the ability to import vulnerability scans from Qualys. This creates a new capability we call vulnerability maps.” The vulnerability map is color-coded from the Qualys data and overlaid on the app dependency map: green is low and informational; orange is medium risk; and red is critical.
But this doesn’t just show the location of the vulnerabilities — added to the app dependency map it shows the potential ramifications of that vulnerability across the network through open ports and connecting and communicating links, and with the internet. These are the paths that an intruder, having exploited a vulnerability, would seek out for lateral movement through the network.
“What we do,” said Glenn, “is combine the Qualys vulnerability data with our application dependency map to let organizations do something they’ve never been able to do before — which is just literally see the data paths within and between data centers in the way a bad actor does, and show the exposure of the vulnerabilities on the hosts. We think this is a transformational moment because traditionally the vulnerability management team and the application team are two different groups. This new approach allows them to collaborate together to do something they haven’t been able to do before: to see how exposed those vulnerabilities actually are.”
Patching individual vulnerabilities may not be immediately possible — but micro-segmenting the network to isolate the vulnerability as far as possible, is possible. Operators can locate the vulnerability, can see the level of criticality, can see and measure paths open to an attacker (something Illumio calls the ‘East-West’ exposure score), and can automatically impose mitigating micro-segmentation controls that limit exposure without breaking any apps.
“Digital transformation leads to an explosion of connected environments where perimeter protection is no longer enough. The focus now needs to shift from securing network perimeters to safeguarding data spread across applications, systems, devices, and the cloud,” says Philippe Courtot, CEO and Chairman of Qualys. “The new Illumio integration with Qualys helps enterprises get visibility across hybrid environments and implement appropriate controls to protect assets from cyber threats, whether on premises or in the cloud.”
If a company has a high value application with a vulnerability that cannot be patched, but the vulnerability management team knows there is a 0-day exploit in the wild (all information courtesy of Qualys), the question becomes, what can be done? “You can use micro-segmentation,” suggests Glenn, “as a way of creating compensating controls to reduce the exposure of the vulnerability. Arbitrarily blocking vulnerabilities is the pathway to breaking applications. So, we’ve created a very nuanced approach, where we look at the connectivity paths that allow us to reduce the exposure without breaking the applications.
“We use the connectivity paths to fine-tune a micro-segmentation policy. It can automatically block or constrain applications. Blocking only ever happens automatically if the ven [Illumio’s virtual enforcement nodes, installed on each host] has never seen traffic on the pathway — perhaps a developer left a port open months ago. Constraining, however, can use micro-segmentation to reduce the effect of a vulnerability without breaking the application. The visible map allows the operator to see the effect of any new policy rules that, once written, will be pushed out to effect the micro-segmentation.”
“Vulnerability management is an invaluable tool in every security team’s arsenal. With our Qualys Cloud Platform integration, organizations can see a map of how active, exposed vulnerabilities can potentially be exploited by a bad actor,” adds Andrew Rubin, CEO and co-founder of Illumio. “By adding vulnerability maps to our Adaptive Security Platform, security teams can see potential attack paths in real time and immediately implement micro-segmentation to prevent the spread of breaches.”
Sunnyvale, Ca-based Illumio raised $100 million Series C financing in April 2015, followed by a further $125 million Series D funding in June 2017.
Related: The Truth About Micro-Segmentation: It’s Not About the Network (Part 1)
Related: The Truth About Micro-Segmentation (Part 2)
Related: The Truth About Micro-Segmentation: Healthy Heterogeneity (Part 3)
Kevin Townsend is a Senior Contributor at SecurityWeek. He has been writing about high tech issues since before the birth of Microsoft. For the last 15 years he has specialized in information security; and has had many thousands of articles published in dozens of different magazines – from The Times and the Financial Times to current and long-gone computer magazines.
Previous Columns by Kevin Townsend:
 Tags:
Tags:
http://feedproxy.google.com/~r/Securityweek/~3/8k7rf1WZ4Dg/illumio-qualys-partner-vulnerability-based-micro-segmentation