
Q Link Wireless, a provider of low-cost mobile phone and data services to 2 million US-based customers, has been making sensitive account data available to anyone who knows a valid phone number on the carrier’s network, an analysis of the company’s account management app shows.
Dania, Florida-based Q Link Wireless is what’s known as a Mobile Virtual Network Operator, meaning it doesn’t operate its own wireless network but rather buys services in bulk from other carriers and resells them. It provides government-subsidized phones and service to low-income consumers through the FCC’s Lifeline Program. It also offers a range of low-cost service plans through its Hello Mobile brand. In 2019, Q Link Wireless said it had 2 million customers.
The carrier offers an app called My Mobile Account (for both iOS and Android) that customers can use to monitor text and minutes histories, data and minute usage, or to buy additional minutes or data. The app also displays the customer’s:
- First and last name
- Home address
- Phone call history (from/to)
- Text message history (from/to)
- Phone carrier account number needed for porting
- Email address
- Last four digits of the associated payment card
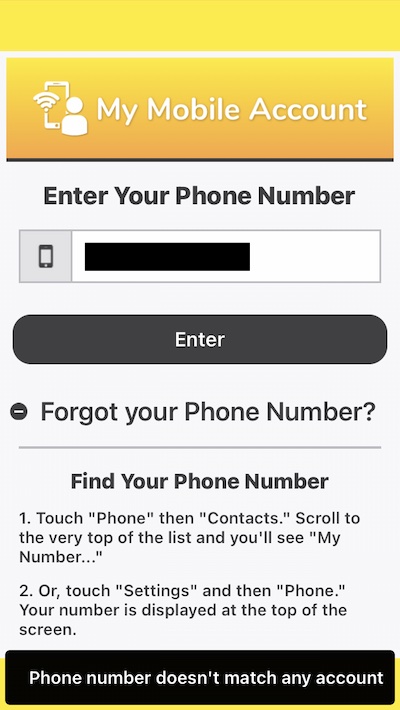
Screenshots from the iOS version look like this:
No password required . . . what?
Since at least December and possibly much earlier, My Mobile Account has been displaying this information for every customer account whenever it is presented with a valid Q Link Wireless phone number. That’s right—no password or anything else required.
When I first saw a Reddit thread discussing the app, I thought for sure there was some kind of mistake. So I installed the app, got the permission from another thread reader, and entered his phone number. I was immediately viewing his personal information, as the redacted images above demonstrate.
The person who started the Reddit thread said in an email that he first reported this glaring insecurity to Q Link Wireless sometime last year. Emails he provided show that he notified support twice again this year, first in February and again this month.
Feedback left in reviews for both the iOS and Android offerings also reported this issue, in several cases with a response from a Q Link Wireless representative thanking the person for the feedback.
Downright negligence
The data exposure is serious because phone numbers are so easy to come by. We give them to prospective employers, car mechanics, and other strangers. And of course, phone numbers are easily obtained by private detectives, abusive spouses, stalkers, and other people who have an interest in a particular person. Q Link Wireless making customer data freely available to anyone who knows a customer’s phone number is an act of downright negligence.
I began emailing the carrier about the insecurity on Wednesday and followed up with almost a dozen more messages. Q Link Wireless CEO and founder Issa Asad didn’t respond despite my noting that every hour he allowed the data exposure to continue compounded the risk to his customers.
Then late on Thursday, My Mobile Account stopped connecting to customers’ accounts. When presented with the number of a Q Link Wireless customer, the app responds with a message saying, “Phone number doesn’t match any account.” The iOS and Android versions of the app were last updated in February, suggesting that the fix is the result of a change Q Link Wireless made to a server.
While My Mobile Account displayed customers’ personal information, it didn’t provide a means to change that data. The app also didn’t display passwords. That means a person couldn’t exploit this leak to perform a SIM swap or lock users out of their accounts, although the exposure might make it easier for a would-be SIM swapper to social engineer a Q Link Wireless employee into porting a number to a new phone.
There are no indications one way or the other that this leakage was actively exploited. Researchers from security firm Intel471 found no discussions in criminal forums about the available data, but there’s no way to know if it was abused on a smaller scale, say by someone a Q Link Wireless customer knows or has interacted with.
As phone users seeking low-cost, no-frills mobile service, Q Link Customers are a part of a population that may be least able to afford data breach services and other privacy services. The carrier has yet to notify customers of the data exposure. People using the service should consider any data displayed by the app to be available to anyone who has their phone number.
https://arstechnica.com/?p=1755853

