
Google has given the boot to nine Android apps downloaded more than 5.8 million times from the company’s Play marketplace after researchers said these apps used a sneaky way to steal users’ Facebook login credentials.
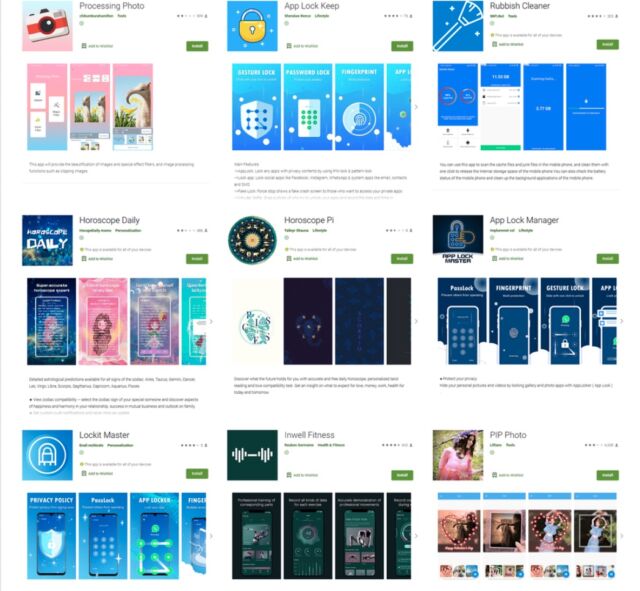
In a bid to win users’ trust and lower their guard, the apps provided fully functioning services for photo editing and framing, exercise and training, horoscopes, and removal of junk files from Android devices, according to a post published by security firm Dr. Web. All of the identified apps offered users an option to disable in-app ads by logging into their Facebook accounts. Users who chose the option saw a genuine Facebook login form containing fields for entering usernames and passwords.
Then, as Dr. Web researchers wrote:
These trojans used a special mechanism to trick their victims. After receiving the necessary settings from one of the C&C servers upon launch, they loaded the legitimate Facebook web page https://www.facebook.com/login.php into WebView. Next, they loaded JavaScript received from the C&C server into the same WebView. This script was directly used to hijack the entered login credentials. After that, this JavaScript, using the methods provided through the JavascriptInterface annotation, passed stolen login and password to the trojan applications, which then transferred the data to the attackers’ C&C server. After the victim logged into their account, the trojans also stole cookies from the current authorization session. Those cookies were also sent to cybercriminals.
Analysis of the malicious programs showed that they all received settings for stealing logins and passwords of Facebook accounts. However, the attackers could have easily changed the trojans’ settings and commanded them to load the web page of another legitimate service. They could have even used a completely fake login form located on a phishing site. Thus, the trojans could have been used to steal logins and passwords from any service.
The researchers identified five malware variants stashed inside the apps. Three of them were native Android apps, and the remaining two used Google’s Flutter framework, which is designed for cross-platform compatibility. Dr. Web said that it classifies all of them as the same trojan because they use identical configuration file formats and identical JavaScript code to steal user data.
Dr. Web identified the variants as:
The majority of the downloads were for an app called PIP Photo, which was accessed more than 5.8 million times. The app with the next greatest reach was Processing Photo, with more than 500,000 downloads. The remaining apps were:
A search of Google Play shows that all apps have been removed from Play. A Google spokesman said that the company has also banned the developers of all nine apps from the store, meaning they will not be allowed to submit new apps. That’s the right thing for Google to do, but it nonetheless poses only a minimal hurdle for the developers because they can simply sign up for a new developer account under a different name for a one-time fee of $25.
Anyone who has downloaded one of the above apps should thoroughly examine their device and their Facebook accounts for any signs of compromise. Downloading a free Android antivirus app from a known security firm and scanning for additional malicious apps isn’t a bad idea, either. The offering from Malwarebytes is my favorite.
https://arstechnica.com/?p=1778045

