
Researchers have uncovered a malicious Android app that can tamper with the wireless router the infected phone is connected to and force the router to send all network devices to malicious sites.
The malicious app, found by Kaspersky, uses a technique known as DNS (Domain Name System) hijacking. Once the app is installed, it connects to the router and attempts to log in to its administrative account by using default or commonly used credentials, such as admin:admin. When successful, the app then changes the DNS server to a malicious one controlled by the attackers. From then on, devices on the network can be directed to imposter sites that mimic legitimate ones but spread malware or log user credentials or other sensitive information.
Capable of spreading widely
“We believe that the discovery of this new DNS changer implementation is very important in terms of security,” Kaspersky researchers wrote. “The attacker can use it to manage all communications from devices using a compromised Wi-Fi router with the rogue DNS settings.”
The researchers continued: “Users connect infected Android devices to free/public Wi-Fi in such places as cafes, bars, libraries, hotels, shopping malls, and airports. When connected to a targeted Wi-Fi model with vulnerable settings, the Android malware will compromise the router and affect other devices as well. As a result, it is capable of spreading widely in the targeted regions.”
DNS is the mechanism that matches a domain name like ArsTechnica.com to 18.188.231.255, the numerical IP address where the site is hosted. DNS lookups are performed by servers operated by a user’s ISP or by services from companies such as Cloudflare or Google. By changing the DNS server address in a router’s administrative panel from a legitimate one to a malicious one, attackers can cause all devices connected to the router to receive malicious domain lookups that lead to lookalike sites used for cybercrime.
The Android app is known as Wroba.o and has been in use for years in various countries, including the US, France, Japan, Germany, Taiwan, and Turkey. Curiously, the DNS hijacking technique the malware is capable of is being used almost exclusively in South Korea. From 2019 to most of 2022, attackers lured targets to malicious sites that were sent through text messages, a technique known as smishing. Late last year, the attackers incorporated DNS hijacking into their activities in that Asian nation.
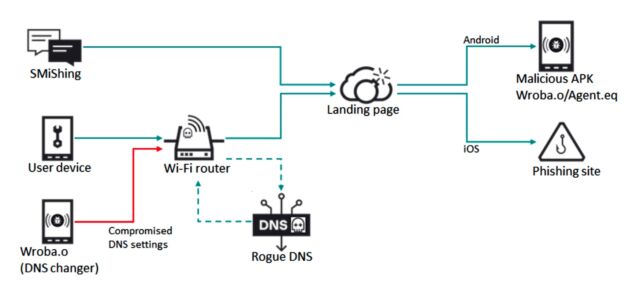
The attackers, known in the security industry as Roaming Mantis, designed the DNS hijacking to work only when devices visit the mobile version of a spoofed website, most likely to ensure the campaign goes undetected.
While the threat is serious, it has a major shortcoming—HTTPS. Transport Layer Security (TLS) certificates that serve as the underpinning for HTTPS bind a domain name such as ArsTechnica.com to a private encryption key that’s known only to the site operator. People directed to a malicious site masquerading as Ars Technica using a modern browser will receive warnings that the connection isn’t secure or will be asked to approve a self-signed certificate, a practice that users should never follow.
Another way to combat the threat is to ensure the password protecting a router’s administrative account is changed from the default one to a strong one.
Still, not everyone is versed in such best practices, which leaves them open to visiting a malicious site that looks almost identical to the legitimate one they intended to access.
“Users with infected Android devices that connect to free or public Wi-Fi networks may spread the malware to other devices on the network if the Wi-Fi network they are connected to is vulnerable,” Thursday’s report stated. “Kaspersky experts are concerned about the potential for the DNS changer to be used to target other regions and cause significant issues.
https://arstechnica.com/?p=1911361

