Researchers have uncovered a massive hacking campaign that’s using sophisticated tools and techniques to compromise the networks of companies around the world.
The hackers, most likely from a well-known group that’s funded by the Chinese government, are outfitted with both off-the-shelf and custom-made tools. One such tool exploits Zerologon, the name given to a Windows server vulnerability, patched in August, that can give attackers instant administrator privileges on vulnerable systems.
Symantec uses the code name Cicada for the group, which is widely believed to be funded by the Chinese government and also carries the monikers of APT10, Stone Panda, and Cloud Hopper from other research organizations. The group, which has no relation to or affiliation with any company using the name Cicada, has been active in espionage-style hacking since at least 2009 and almost exclusively targets companies linked to Japan. While the companies targeted in the recent campaign are located in the United States and other countries, all of them have links to Japan or Japanese companies.
On the lookout
“Japan-linked organizations need to be on alert as it is clear they are a key target of this sophisticated and well-resourced group, with the automotive industry seemingly a key target in this attack campaign,” researchers from security firm Symantec wrote in a report. “However, with the wide range of industries targeted by these attacks, Japanese organizations in all sectors need to be aware that they are at risk of this kind of activity.”
The attacks make extensive use of DLL side-loading, a technique that occurs when attackers replace a legitimate Windows dynamic-link library file with a malicious one. Attackers use DLL side-loading to inject malware into legitimate processes so they can keep the hack from being detected by security software.
The campaign also makes use of a tool that’s capable of exploiting Zerologon. Exploits work by sending a string of zeros in a series of messages that use the Netlogon protocol, which Windows servers use to let users log in to networks. People with no authentication can use Zerologon to access an organization’s crown jewels—the Active Directory domain controllers that act as an all-powerful gatekeeper for all machines connected to a network.
Microsoft patched the critical privilege-escalation vulnerability in August, but since then attackers have been using it to compromise organizations that have yet to install the update. Both the FBI and Department of Homeland Security have urged that systems be patched immediately.
Among the machines compromised during attacks discovered by Symantec were domain controllers and file servers. Company researchers also uncovered evidence of files being exfiltrated from some of the compromised machines.
Multiple regions and industries
Targets come from a variety of industries, including:
- Automotive, with some manufacturers and organizations involved in supplying parts to the motor industry also targeted, indicating that this is a sector of strong interest to the attackers
- Clothing
- Conglomerates
- Electronics
- Engineering
- General Trading Companies
- Government
- Industrial Products
- Managed Service Providers
- Manufacturing
- Pharmaceutical
- Professional Services
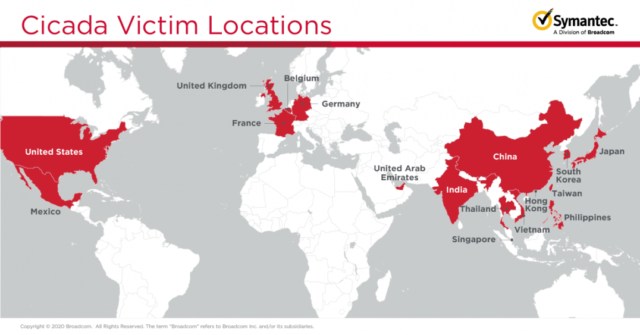
Below is a map of the physical location of the targets:
Symantec linked the attacks to Cicada based on digital fingerprints found in the malware and attack code. The fingerprints included obfuscation techniques and shell code involved in the DLL side-loading as well as the following traits noted in this 2019 report from security firm Cylance:
- Third-stage DLL has an export named “FuckYouAnti”
- Third-stage DLL uses CppHostCLR technique to inject and execute the .NET loader assembly
- .NET Loader is obfuscated with ConfuserEx v1.0.0
- Final payload is QuasarRAT—an open source backdoor used by Cicada in the past
“The scale of the operations also points to a group of Cicada’s size and capabilities,” the Symantec researchers wrote. “The targeting of multiple large organizations in different geographies at the same time would require a lot of resources and skills that are generally only seen in nation-state backed groups. The link all the victims have to Japan also points towards Cicada, which has been known to target Japanese organizations in the past.”
https://arstechnica.com/?p=1724195

