
Microsoft has patched a critical zero-day vulnerability that North Korean hackers were using to target security researchers with malware.
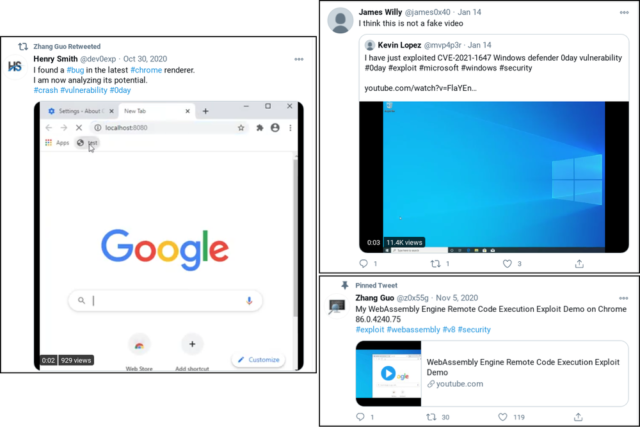
The in-the-wild attacks came to light in January in posts from Google and Microsoft. Hackers backed by the North Korean government, both posts said, spent weeks developing working relationships with security researchers. To win the researchers’ trust, the hackers created a research blog and Twitter personas who contacted researchers to ask if they wanted to collaborate on a project.
Eventually, the fake Twitter profiles asked the researchers to use Internet Explorer to open a webpage. Those who took the bait would find that their fully patched Windows 10 machine installed a malicious service and an in-memory backdoor that contacted a hacker-controlled server.
Microsoft on Tuesday patched the vulnerability. CVE-2021-26411, as the security flaw is tracked, is rated critical and requires only low-complexity attack code to exploit.
From rags to riches
Google said only that the people who reached out to the researchers worked for the North Korean government. Microsoft said they were part of Zinc, Microsoft’s name for a threat group that is better known as Lazarus. Over the past decade, Lazarus has transformed from a ragtag group of hackers to what can often be a formidable threat actor.
A United Nations report from 2019 reportedly estimated Lazarus and associated groups have generated $2 billion for the country’s weapons of mass destruction programs. Lazarus has also been tied to the Wannacry worm that shut down computers around the world, fileless Mac malware, malware that targets ATMs, and malicious Google Play apps that targeted defectors.
Besides using the watering-hole attack that exploited IE, the Lazarus hackers who targeted the researchers also sent targets a Visual Studio Project purportedly containing source code for a proof-of-concept exploit. Stashed inside the project was custom malware that contacted the attackers’ control server.
While Microsoft describes CVE-2021-26411 as an “Internet Explorer Memory Corruption Vulnerability,” Monday’s advisory says the vulnerability also affects Edge, a browser Microsoft built from scratch that’s considerably more secure than IE. The vulnerability retains its critical rating for Edge, but there are no reports that exploits have actively targeted users of that browser.
The patch came as part of Microsoft’s Update Tuesday. In all, Microsoft issued 89 patches. Besides the IE vulnerability, a separate escalation privilege flaw in the Win32k component is also under active exploit. Patches will install automatically over the next day or two. Those who want the updates immediately should go to Start > settings (the gear icon) > Update & Security > Windows Update.
https://arstechnica.com/?p=1748406

