
Iranian state hackers got caught with their pants down recently when researchers uncovered more than 40GB of data, including training videos showing how operatives hack adversaries’ online accounts and then cover their tracks.
The operatives belonged to ITG18, a hacking group that overlaps with another outfit alternatively known as Charming Kitten and Phosphorous, which researchers believe also works on behalf of the Iranian government. The affiliation has long targeted US presidential campaigns and US government officials. In recent weeks, ITG18 has also targeted pharmaceutical companies. Researchers generally consider it a determined and persistent group that invests heavily in new tools and infrastructure.
In May, IBM’s X-Force IRIS security team obtained the 40GB cache of data as it was being uploaded to a server that hosted multiple domains known to be used earlier this year by ITG18. The most telling contents were training videos that captured the group’s tactics, techniques, and procedures as group members performed real hacks on email and social media accounts belonging to adversaries.
Included in the footage was:
- Almost five hours of video showing operators searching through and exfiltrating data from multiple compromised accounts belonging to two people, one a member of the US Navy and the other a seasoned personnel officer in the Hellenic Navy.
- Failed phishing attempts that targeted US State Department officials and an Iranian American philanthropist. The failures were the result of emails bouncing because they appeared suspicious.
- Online personas and Iranian phone numbers used by group members.
The haul of data is a potential intelligence coup because it allows researchers (and presumably US officials) to identify the strengths and weaknesses of an adversary that is steadily improving its hacking talent. Defenders can then improve protections designed to keep the attackers out. The bird’s-eye view may also have signaled plans for future ITG18 operations.
A rare opportunity
“Rarely are there opportunities to understand how the operator behaves behind the keyboard, and even rarer still are there recordings the operator self-produced showing their operations,” IBM researchers Allison Wikoff and Richard Emerson wrote in a post published Thursday. “But that is exactly what X-Force IRIS uncovered on an ITG18 operator whose OPSEC failures provide a unique behind-the-scenes look into their methods, and potentially, their legwork for a broader operation that is likely underway.”
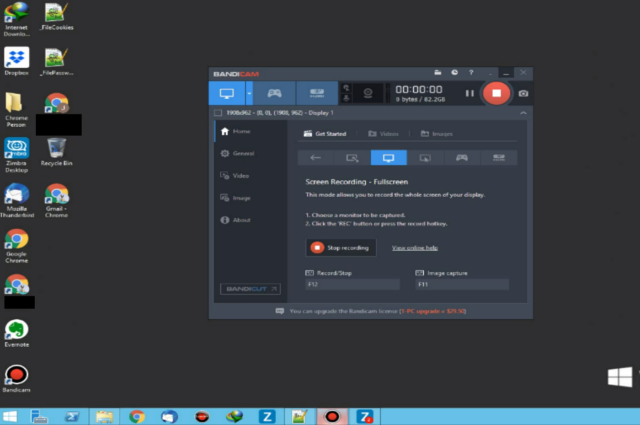
The videos were shot using a desktop recording tool called Bandicam and ranged from two minutes to two hours. Timestamps indicated the videos were recorded a day or so before they were uploaded. Five of the videos showed operators pasting passwords into compromised accounts and then demonstrating how to efficiently exfiltrate contacts, photos, and other data stored there and in associated cloud storage.
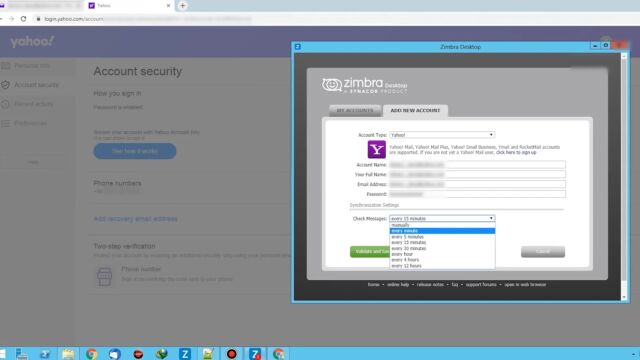
The footage also showed the settings that group members changed in the security configurations of each compromised account. The changes allowed the hackers to connect some of the accounts to Zimbra, an email collaboration program that can aggregate multiple accounts into a single interface. Using Zimbra made it possible to manage hacked email accounts simultaneously.
Three other videos revealed that the operators had compromised several accounts associated with an enlisted member of the US Navy and an officer in the Hellenic Navy. ITG18 members had credentials for what appear to be their personal email and social media accounts. In many cases, the hackers deleted emails notifying the targets that there had been suspicious logins to their accounts.
Painstaking detail
The attackers also accessed files showing the military units the Navy personnel were in, their naval base, residence, personal photos and videos, and tax records. The operators methodically combed through targets’ other accounts, including those on video-streaming sites, pizza-delivery services, credit-reporting agencies, mobile carriers, and more.
“The operators appear to have been meticulously gathering trivial social information about the individuals,” the IBM researchers wrote. “In total, the operator attempted to validate credentials for at least 75 different websites across the two individuals.
Other videos displayed the Iran-based phone number and other profile details for a fake persona ITG18 members used in their operations. The video also revealed attempts to send phishing emails to the Iranian American philanthropist and two possible State Department officials.
Another potentially useful discovery: when operators used a password to successfully gain initial access to an account that was protected by multifactor authentication, they would proceed no further. That suggests that Charming Kitten’s previously revealed ability to bypass multifactor authentication is limited.
The behind-the-scenes account IBM obtained demonstrates the double-edged sword that’s wielded by espionage hackers. While their operations often yield useful information on their targets, the targets can also turn that around in Spy vs. Spy fashion.
https://arstechnica.com/?p=1692490

